🚨OH MY GOSH!!!
— Matt Van Swol (@mattvanswol) April 29, 2026
Two police officers were HOSPITALIZED and 9 people were arrested when over 1,000 "teens" rushed ICON Park in Orlando FL for a "teen-takeover" event.
Parents of the teens are now demanding POLICE OFFICERS BE SUSPENDED for "unnecessary force…"
WHAT??!!!!!! pic.twitter.com/wnJi03QCgA
Ivermectin Dosages
Free PDF Download of The Great Taking
The New Declaration of Independence
AppalachianRenegade YouTube Channel
Free PDF Download of The Great Taking
The New Declaration of Independence
AppalachianRenegade YouTube Channel
State collapse is inevitable when a society’s leaders are insulated from the negative consequences of their bad decisions.
Mike Shelby
Latest Articles
Click on the Title of the Article to View or Add Comments
-
Orlando
-
Ft. Knox Full Of Impure Gold Unfit For International Transactions
The bulk of the US gold reserves held in Fort Knox are made up of impure “non-standard” bars that don’t qualify for use in international settlements.
In practice, this means that most of America’s massive gold stockpile is illiquid and wouldn’t be readily accepted on the international market should the need arise:
“It’s a decrepit relic just like our monetary policy is. With respect to America’s gold stockpile, we hold ourselves to a lower standard than the rest of the world,” Money Metals CEO Stefan Gleason said.
Mises Institute Editor in Chief Ryan McMaken called the US gold reserves “a legacy of theft and lies,” pointing out that the gold reserve was never intended to be a “static, untouchable hoard of the US government.” -
Paper Tiger
-
The Spirit of Freedom

In the mist of the first dawns, when the world still trembled between fire and ice, a spirit rose from the ancient forests of the North. The storms did not bear his name, yet the mountains remembered his voice. He was called the Spirit of Freedom.
He was not a god like the others. He was older—born from the very first breath of the earth itself, when humankind did not yet know that they could wear chains. In the hearts of the early tribes, he flickered like an invisible fire, untamed and wild.
When warriors stood beneath dark clouds, they felt him in the thunder. When women sang by the river, they heard him in the rushing water. And when a child first entered the forest and knew no fear, it was because this spirit awoke within them.
But time brought shadows. Chains were forged—not only of iron, but of fear, of doubt, of the desire for domination. The old songs fell silent, and the spirit of freedom withdrew, deep into the roots of the world.
There it still waits.
It is said that it returns when a person finds the courage to stand up against injustice, when someone follows their own path even though the world tries to stop them. Then the ancient fire flares up again—quietly at first, then unstoppably.
For the Germanic spirit is not a relic of bygone times.
It is the spirit of freedom—and it lives in everyone who refuses to be broken.From Huter der Irminsul
-
Time to Stand
We weren’t born in this age to wring our hands, shuffle our feet and bow our heads as our lessers rape, murder and destroy our race and world. Nor do I believe that fate has been written and defeat is certain.
This is our age to prove that our race deserves to live. Nature is testing us, and men and women smarter than me have already laid the philosophical groundwork for even I to understand that nature selects for action and movement and ferocity and sheer fucking will.
We’re being laughed at by our enemies while the divines look on us and surely must be saying “Well come on, then!” Because they can only do so much, and we have to do our part now.
This is our time to be heroes for those that come after us!AnthasGate
-
Meanwhile in Cuba
-
Comey Indicted
-
The “Kill” Switch
From Dr. Robert Malone: The real question is not whether someone can flip a switch and stop your car. It is whether you still meaningfully control the terms under which you are allowed to drive it.
… and from the Fyrgen in the UK …
Things seem to be changing on the Digital ID front whilst we’re all distracted by Iran and fuel prices.
Reluctantly, due to work, I tried to create a new gmail address today. It’s no longer possible to do without a phone, because Google demands that you verify identity using a smartphone.
Whilst trying to find a loophole, I saw this help article (screenshot, above).
I also heard today that UK Parliament has voted in favour of restricted Internet access for under-16s (https://www.bbc.co.uk/news/articles/c5y7d2zx63jo). Of course, the real reason is to require people of all ages to show proof of age/identity before accessing the Internet, which will quickly become a requirement.
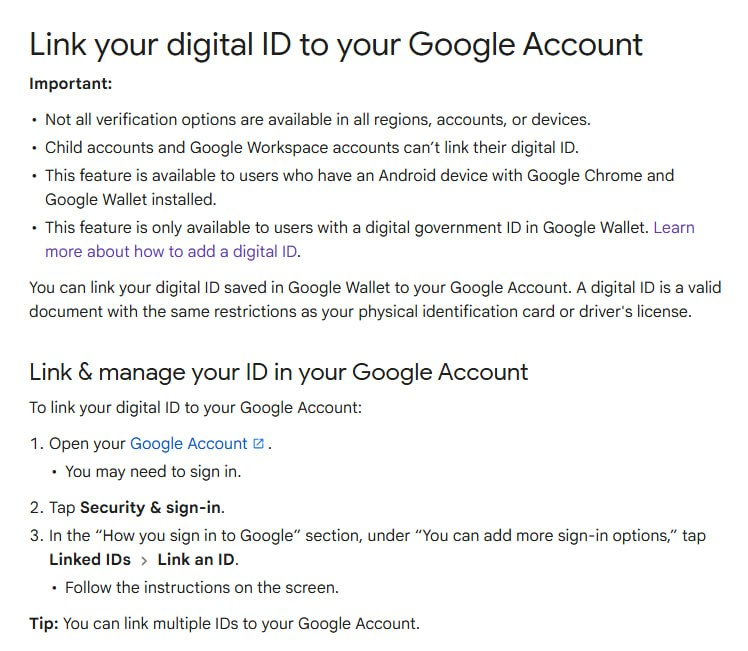
The brutal truth is that almost none of the millions of people who ‘say no to digital ID’ will actually avoid digital ID. It’s already here, and if in a month’s time we all have to prove our identity to access the Internet, who will say ‘no’?
I wouldn’t be able to say ‘no’, because as things stand, I rely partially on the Internet to feed my family. if you’re able to say ‘no’, more power to you. May you stand forever.
We should have been figuring out years ago how to make money offline, how to manage money offline, how to shop offline, how to socialise offline, how to be entertained offline.
It’s never too late to figure that stuff out, but it becomes harder to escape once we’ve already surrendered to it and bought ourselves the convenience of compliance.
The time is close at hand that one will have to decide whether to abandon the internet and newer cars. Freedom isn’t free …
-
Will OPEC Survive?
-
There It Is …

-
The Lost Cause

Upon the Soviet Union’s dismissal of 146 historians from Czech universities, Milan Hübl, among those dismissed, is said to have observed, “The first step in liquidating a people is to erase its memory.” Hübl went on to predict that after a “new history” takes the place of the old “the nation will begin to forget what it is and what it was.”[1] Such sentiment echoed a similar southern fear during and after the American Civil War. Confederate General Patrick Cleburne declared that, “Surrender means that the history of this heroic struggle will be written by the enemy; that our youth will be trained by northern school teachers; will learn from northern school books their version of the War; will be impressed by all the influences of history and education to regard our gallant dead as traitors, and our maimed veterans as fit subjects for derision.”
… and so, here we are. They’ve even now destroyed our monuments.
Read the entire Abbeville Institute essay.
My great grandfather enlisted in Confederate service at age sixteen and returned from the war with a Yankee ball in his knee. I personally view my country as having been invaded, conquered, and occupied by a foreign army. My country is still occupied to this day. I remain unrepentant and unreconstructed. Teach what they will, my children and grandchildren know the truth.
In some ways, Patrick Cleburne’s concern that southern children would learn the northern “version of the War” to the point of regarding Confederate soldiers as “fit subjects for derision” has taken place in urban areas of the South. However, in small towns and rural areas the Confederate ghost, the moonlight and magnolias, and indeed, the “Myth of the Lost Cause” still continues to endure. Or perhaps it is not a myth at all. Maybe Jefferson Davis was right when he was said to have remarked after the war, “Truth crushed to the earth is truth still and like a seed will rise again.”
-
Act Like Men
-
The Truth Is Coming Out
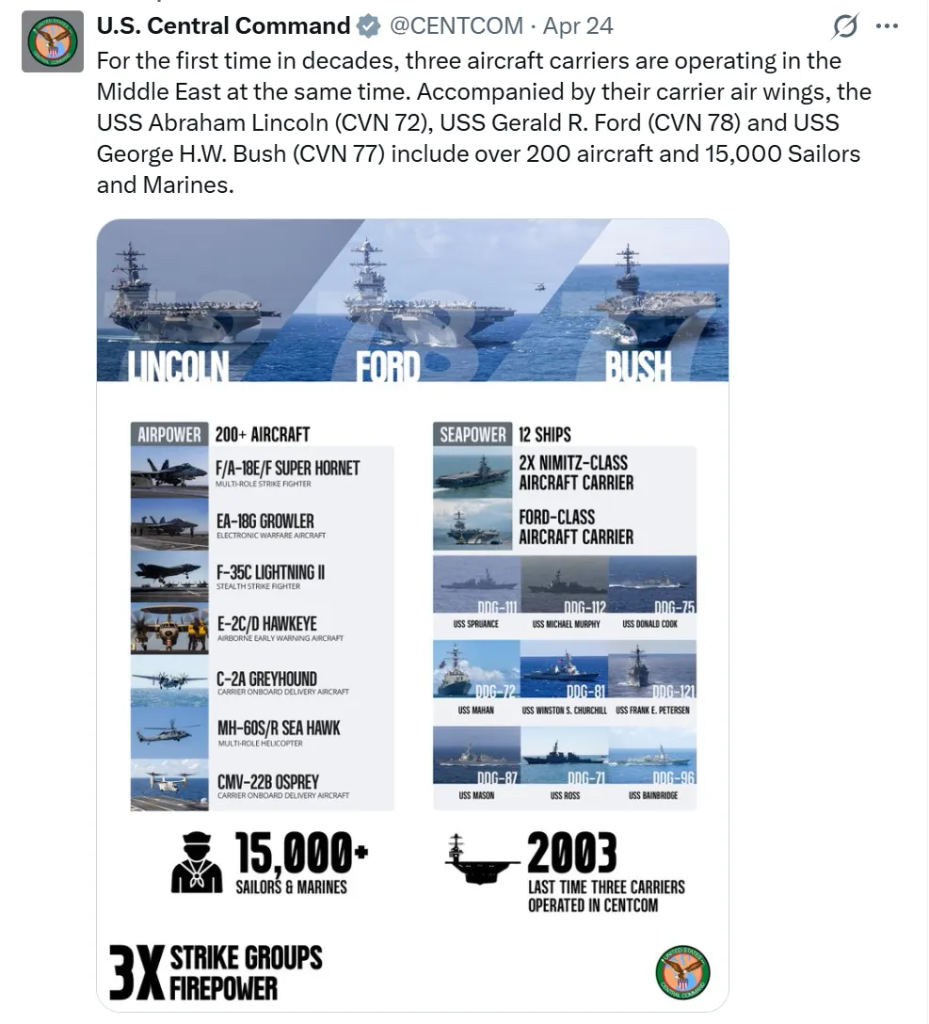
Simplicius notes the truth of the actual damage done to US bases early in the war. Things pundits like Mcgregor, Johnson, Crooke, and company were accurately reporting, but Fox News rejected.
Putting two and two together we can now reconstruct the events more accurately: Iranian aircraft appeared to have breached US defenses, directly gravity-bombed US bases, all while causing flustered defenders to engage in friendly fire. That means Iran was able to do to the US what even Ukraine has not been able to do to Russia, despite Ukraine having a more modern NATO-supplied airforce.
… and …
Rubio makes what might be the worst and stupidest logical equivalencies imaginable. First, he says Iran’s hostage-taking of the Strait of Hormuz is akin to a “nuclear weapon”, then outdoes his own imbecility by concluding that Iran’s Hormuz actions mean that if Iran were to have nuclear weapons, it would use them against the world:
By that logic, since the lowest cumulative IQ US administration in history has also chosen to blockade Hormuz, and since the US does already possess nuclear weapons and has even used them against peaceful civilians in the past, we should therefore make the natural ‘ergo’ assumption.
In fact, what Rubio and the rest of his juvenile administration are doing is grasping at straws to make any even remotely frail argument that could be sold to the American gorms as some kind of justification for the Israel-servitude we are witnessing. It’s as specious and hollow as Trump claiming the Iran war was necessary now—of all times—because “Iran had been threatening America for 47 years”.
It’s simply embarrassing.
-
“You Can Vote Your Way Into Socialism, but You Have To Shoot Your Way Out.”
-
Israeli War Crimes
Menu
CADD Graphics
Carolina Readiness Supply
Social Media and Websites
NC Renegade on TwitterNC Renegade on Gab
NC Renegade on Truth Social
Wes Rhinier on Gab
12 Round Blog
Barnhardt
Cold Fury
The Feral Irishman
Hammer’s Thor
Knuckledraggin My Life Away
Liberty’s Torch
90 Miles From Tyranny
Publius-Huldah’s Blog
Smoky Mountain Myco
Straight Line Logic
The Tactical Hermit
Western Rifle Shooters Association
Recent Comments
What they are telling us, is they want us dead and gone. Pretty clear to me, LOCK AND LOAD TINVOWOOT.
Who put up the $500 (assuming 10% down was required) for him to meet bond? Just asking.
I’m fully onboard with this.
First thing I thought was they are off celebrating Commie day, what a surprise..



Tom, she is a black tribal a hole looting our treasury like all her ilk do. I would suggest her…